Artificial intelligence is no longer a theoretical experiment. It already drives critical operational decisions, from fraud detection and patient journey management to energy infrastructure operations. In this context, sovereignty is no longer an abstract concept. It becomes a practical requirement for deploying AI with confidence.
Data & AI Trends for 2026: Governance, Regulation, Sovereignty and the Shift to Autonomous AI
See moreSovereignty as a condition for AI deployment
Who controls the data? Who can explain an automated decision and prove compliance to an auditor or regulator? These questions determine whether an organization can deploy AI at scale with confidence.
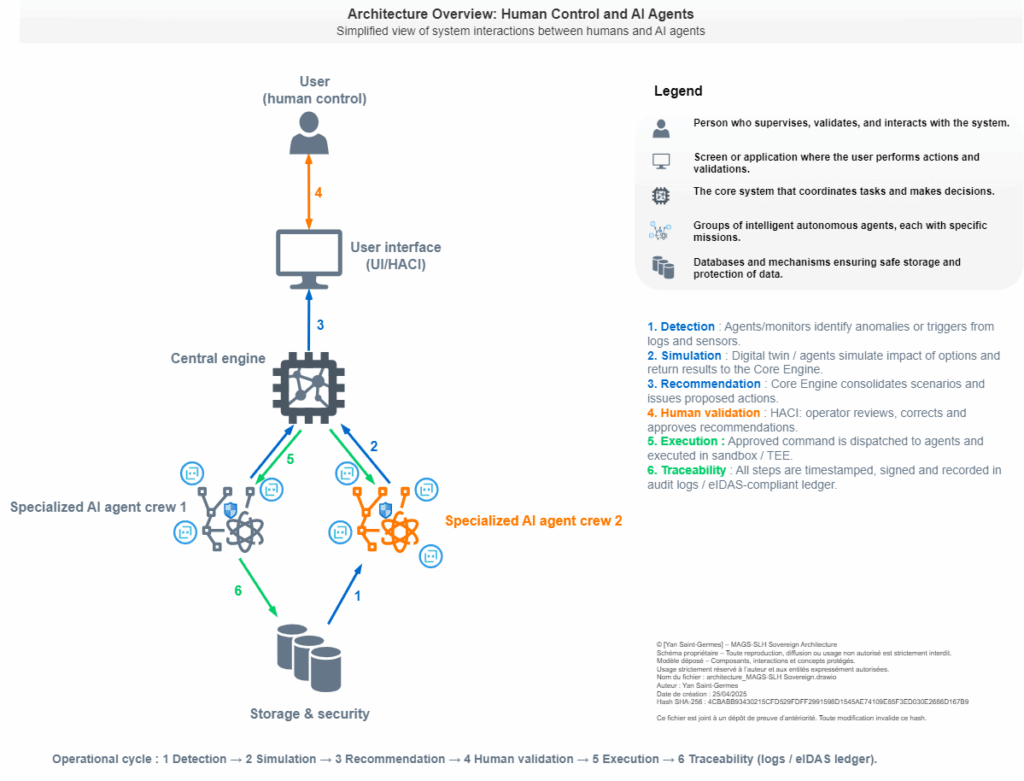
This is exactly what the MAGS-SLH Sovereign pattern aims to address. Behind this name is an innovative architecture designed to orchestrate critical AI systems in a secure, compliant and transparent environment. It integrates advanced mechanisms for human oversight, traceability and resilience to ensure trust and regulatory compliance. The goal is to keep people and traceability at the center of AI systems while still benefiting from automation.

The risks that require rethinking architecture are real and numerous
First, there is technological dependency. Entrusting sensitive data to platforms located outside a sovereign environment can expose organizations to legal and operational risks. It can also create vulnerabilities linked to potential service disruptions or unfavorable contractual conditions.
Another challenge is decision opacity, which is both a practical and legal issue. Without certified logging and clear explanations, it becomes difficult to demonstrate that an automated decision complies with regulations during an audit or a dispute.
Active attacks are also increasing, including prompt injections, multi-agent manipulation and counterfeiting within execution environments. At the same time, the European regulatory framework such as GDPR, DORA, NIS2, eIDAS and the Cyber Resilience Act requires strong auditability, proof retention and control over where data is processed. Faced with these combined challenges, focusing only on the AI model is no longer enough. Organizations need architectures that integrate sovereignty, security and governance from the start.
Using open source solutions can help reduce decision opacity. Publicly audited code and models make it easier to explain how systems work and allow internal or external experts to review them. Open source is also a strong lever for sovereignty. It improves transparency and auditability of critical components while making integration easier and allowing sovereign operators to take control when needed.
Shadow AI, sovereignty, trust: addressing the real challenges of AI
See moreTangible benefits of a sovereign architecture
A sovereign architecture for AI does not mean limiting innovation. Instead, it provides a structured engineering framework that helps turn AI into a reliable and trusted asset.
In the MAGS-SLH Sovereign pattern, sovereignty is built into the architecture itself. Sensitive data cannot be transferred outside controlled environments. Critical operations run inside secure enclaves called Trusted Execution Environments (TEE), which protect data and processing from external interference. In addition, every action is recorded through certified and immutable logging aligned with eIDAS requirements. This ensures full traceability and makes it possible to demonstrate compliance during audits.
The architecture also introduces dynamically generated ephemeral AI agents. These agents can be automatically regenerated when needed, which helps limit the impact of failures or unexpected behavior. Each critical decision goes through a human oversight loop through the HACI interface, the Human-in-the-Loop Arbitrated Cognitive Interface. This process includes impact simulations and a distributed validation mechanism called Proof of Quality (PoQ).
Collaboration between entities can also take place without sharing raw data. Instead, the system relies on anonymized and signed signals called “pheromones.” This approach makes it possible to coordinate intelligence and cooperation between systems while preserving data confidentiality.
To deliver these benefits in practice, organizations can rely on mature open source building blocks such as orchestration tools, private ledgers, observability solutions and machine learning frameworks. These technologies provide a solid, testable and reusable foundation that can also support strict compliance requirements.
Beyond federated learning and sovereign cloud environments, other approaches can also strengthen the model. Distributed coordination methods such as Swarm or Swarm Learning enable collaboration between agents without centralizing data. Open source MLOps platforms like Kubeflow and MLflow also provide practical components that can be integrated into the architecture to manage and scale AI systems efficiently.
It is also worth noting that some existing approaches already move in this direction. Federated Learning, for example, enables distributed model training without centralizing data. Sovereign cloud initiatives such as Gaia-X and open source technology stacks also aim to ensure more controlled and trusted hosting environments.
MAGS-SLH does not aim to reinvent these building blocks. Instead, it brings them together and fills key gaps to create a more complete framework for operational sovereignty. This includes end-to-end eIDAS-compliant logging, systematic human oversight through HACI, the Proof of Quality validation mechanism and the orchestration of ephemeral AI agents. Confidential computing, through Trusted Execution Environments, also strengthens the architecture by protecting sensitive operations during execution. However, it should be considered as a complementary layer rather than the only guarantee of governance.
MAGS-SLH Sovereign at a glance
User interaction through HACI, a central engine, squads of ephemeral AI agents and secure storage. The numbered arrows illustrate the cycle: detection → simulation → recommendation → human validation → execution → traceability.
Practical applications across business use case
Practical applications can already be seen in simple but meaningful scenarios. In the banking sector, fraud detection can benefit from cooperation between subsidiaries. Each entity analyzes its transactions locally and only shares anonymized signals. Emerging correlations can then trigger a human review before any blocking action is taken.
In hospitals, a modification to a sensitive patient record can first be simulated in a digital twin. The proposed action is explained to the practitioner through HACI, executed within a Trusted Execution Environment and recorded with tamper-proof traceability. This approach protects patient privacy while providing strong proof in case of an audit.
For an energy operator, the architecture can orchestrate a team of AI agents to analyze a crisis situation, simulate different scenarios and propose action plans validated by humans. This helps ensure service continuity while maintaining full traceability for regulators.
Many sector pilots already rely on open source tools for orchestration and monitoring to prototype sovereign solutions. This makes proofs of concept easier to reproduce and supports the transition to operational deployment at scale.
European Identity Wallet and Business Wallet: Building Digital Trust in Europe
See moreTrade-offs to anticipate
Adopting a sovereign architecture also involves measured trade-offs. Greater modularity and multiple control layers increase operational complexity. This requires strong orchestration and teams with the right level of expertise. Simulation and validation steps can also introduce some latency. The key is to carefully define when human oversight is required so that the loop is only triggered for truly sensitive actions.
The initial investment can also be higher, particularly for Trusted Execution Environments, certified logging and the integration of external tools. However, this cost is largely offset by reduced regulatory risk, fewer incidents and stronger trust between organizations, users and regulators.
The objective is to achieve application and operational sovereignty. This means maintaining control over code, processes, data, encryption keys and audit evidence. Several key measures should be considered from the design stage.
These include software signing, software bills of materials and software attestation. Key management should remain under customer control through a KMS or within a sovereign cloud. Logging must be immutable and compatible with eIDAS to provide reliable audit evidence. Secure CI/CD pipelines and automated tests for compliance and vulnerabilities are also essential. In addition, strict contractual clauses such as audit rights, vulnerability notifications and regular certifications help reinforce trust and accountability.
Together, these measures support strong operational sovereignty without necessarily addressing the hardware layer. A good practice is to maintain full control over the software supply chain through CI/CD. Managing software bills of materials, signatures, dependencies and automated security scans helps reduce exposure, even when relying on open source components.
Open source can reduce certain costs and risks, especially by improving interoperability and enabling independent audits. However, it also requires proper governance. Version management, dependency security and service level agreements through partners or commercial distributions should be planned from the start of each project.
A pragmatic operational roadmap
The roadmap starts with mapping critical areas, including processes, sensitive data and regulatory obligations. The next step is to prioritize the first use cases to “sovereignize,” focusing on those that combine high value and high risk, such as payment systems, patient records or infrastructure monitoring. A limited pilot phase, typically a three to six month proof of concept on a specific use case, helps validate key components such as the Core Engine, HACI and eIDAS-compliant logging, while also refining the human interface.
Operational indicators should then be monitored closely. These include the mean time to recovery for anomalies, the percentage of sensitive decisions validated by humans and compliance with the rule of zero uncontrolled transfer of sensitive data. From there, the approach can be scaled through reusable components and a governance model that brings together business teams, security and compliance.
Thinking sovereign does not mean stepping away from innovation
The goal is to create the right conditions for AI to become easy to use, auditable and widely accepted. Organizations that succeed in this transition will combine strong technical control, compliance by design and operational pragmatism. The MAGS-SLH Sovereign pattern provides a practical roadmap to transform AI from a regulatory risk into a sustainable strategic asset.
Open source also plays an important role in accelerating sovereign innovation. It allows organizations to share secure building blocks, engage expert communities and maintain technical traceability that aligns with regulatory requirements.










Comments (0)
Your email address is only used by Business & Decision, the controller, to process your request and to send any Business & Decision communication related to your request only. Learn more about managing your data and your rights.