The login journey is a critical moment in the digital experience. As the first point of contact between the user and the service, it is also a potential entry point for cyberattacks and fraud. Yet traditional authentication methods, such as passwords or two-factor authentication, are now showing their limits. How can web authentication and decentralized identity improve security while simplifying user experience by eliminating passwords?
Did you know?
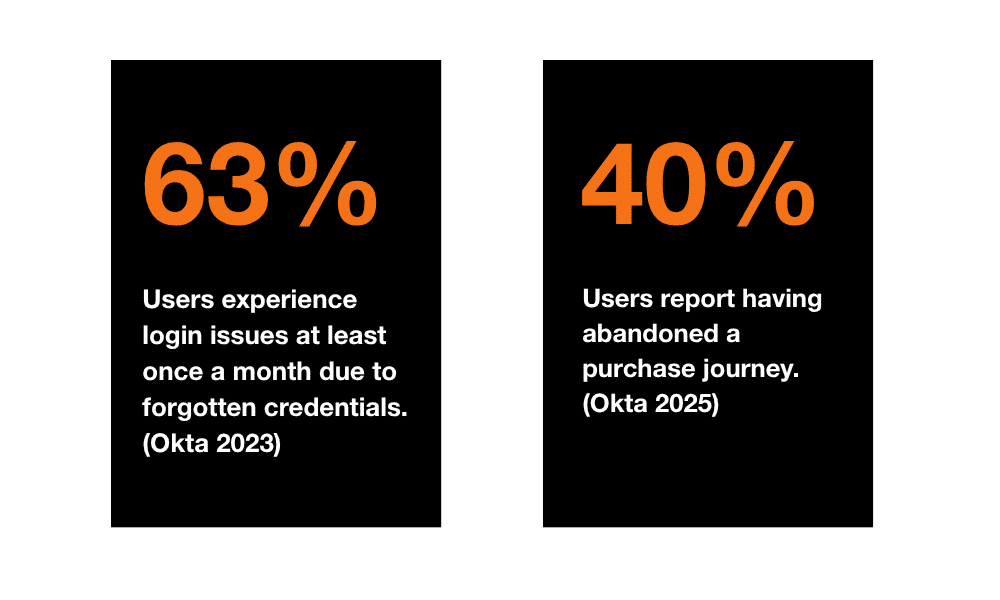
Friction caused by traditional authentication methods affects both user experience and trust in digital services.
To address these challenges, Europe is promoting a more innovative, user-centric approach:
Decentralized digital identity
Verifiable Credentials (VCs)
Supported by European regulation, notably eIDAS 2.0, and set to become mandatory for some use cases by the end of 2027, these technologies enable more secure and seamless authentication without compromising ease of use.
The aim of this article is to clarify the key concepts behind the login journey, explore the benefits of decentralized digital identity for both users and organizations, and explain in simple terms how this approach secures user journeys while preserving a smooth experience.

Overview of login journeys
Identification, authentication and authorization: clarifying the concepts
Three key steps define the login journey
| Concept | Definition | Example | Associated question |
| Identification | Process of recognizing a user or a device | Email address, phone number, unique identifier | Who are you? |
| Authentication | Verification that the user is who they claim to be | Password, biometrics, OTP code, social login | Prove that you are who you claim to be. |
| Authorization | Verification of permissions to access specific resources | Different access rights depending on roles (e.g. read-only vs. full access) | What are you allowed to do? |
The challenge is to provide:
- Clear identification, with no ambiguity about the user’s identity.
- Robust authentication, without making the journey heavier.
- Appropriate authorization, to reduce risk while maintaining a smooth experience.
Les limites des méthodes d’authentification traditionnelles
Traditional authentication methods are now reaching their limits in the face of growing security and user experience requirements.
As highlighted in many reports, these methods no longer meet today’s expectations in terms of security and usability. It is time to consider more robust and seamless alternatives.
Summary of the main challenges encountered
| Method | Main advantage | Limitations | Risks |
| Passwords | Easy to implement | Complex credential management for users, frequent forgetting Lack of resistance to attacks | Increased vulnerability (phishing, brute force) Password reuse (80% of data breaches are linked to compromised credentials) |
| Multi-factor authentication (MFA) | Enhanced security | Complexity for users (SMS codes, authentication apps) CNIL 2025: sending a code by email is no longer considered strong authentication ANSSI: possible SMS interception | Additional costs (SMS delivery, token management) Friction in the user experience |
| Social Login | Ease of use | Data centralization (dependency on major web platforms) | Exposure to data breaches (a compromised account can impact multiple services) |
Decentralized Identity and the EUDI Wallet: a new approach that combines security and user experience
What is decentralized identity?
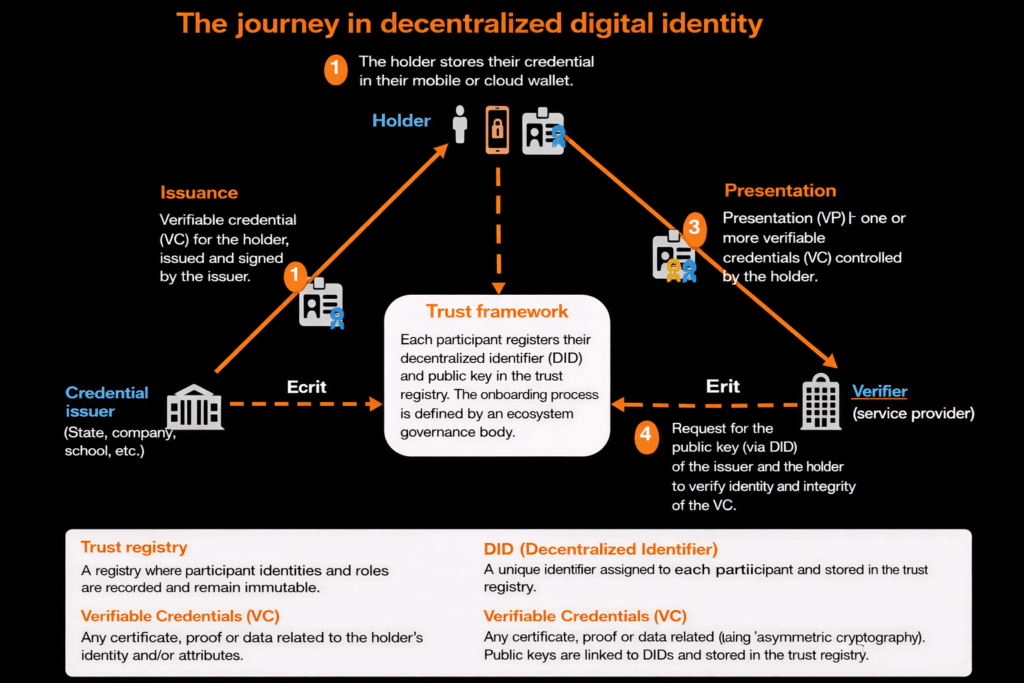
- To address these limitations, decentralized identity, also known as Self-Sovereign Identity (SSI), is emerging as a promising alternative. Unlike traditional systems where a centralized provider manages identity, SSI is based on several key components.
- Decentralized Identifiers (DIDs) are unique and tamper-proof identifiers.
- Verifiable Credentials (VCs) are cryptographically secured digital attestations that allow information to be verified without relying on centralized databases, for example a digital driver’s license, an employee certificate or a company registration document.
- Key benefits include reduced data sharing, portability of credentials, user control and decentralized verification.
- Finally, an identity wallet allows users to securely store and share their credentials.
The European digital identity
Among the solutions based on decentralized identity are the European Digital Identity Wallet (EUDI Wallet) for citizens and the European Business Wallet for organizations. These key European Union initiatives aim to:
- Enable every citizen and business to have a digital identity
- Strengthen identity security through cryptographic authentication and high assurance levels at onboarding
- Simplify digital journeys with passwordless login, KYC, KYS and KYE processes, and identity attribute verification
- Protect privacy by giving users full control over the data they choose to share
By 2030, 80% of European citizens are expected to have a secure digital identity through the EUDI Wallet.
European Commission, 2023
The emergence and adoption of this approach are driven by the eIDAS 2 regulation. The acceptance of the EUDI Wallet in authentication journeys will become mandatory by the end of 2027 for large online platforms, certain public services and some private companies where strong authentication is required by law.
Current authentication systems, such as passwords, MFA or social login, will need to evolve to recognize and leverage identities provided through these wallets.
The added value of digital identity and its complementarity with existing solutions
Comparaison des solutions d’authentification
| Solution | Security | User experience | Interoperability | Portability |
| Passwords | Low | Medium (friction due to forgotten credentials) | Limited | No |
| MFA (SMS or email) | Medium | Medium (complexity in the journey) | Medium | No |
| Social Login | Medium | Excellent (one-click login) | High | Yes (but dependent on third-party providers) |
| Decentralized identity (VC) | Very high | Excellent (user control) | High | Yes |
Digital identity solutions offer at least three key benefits:
- Enhanced security: decentralized verification and digital credentials reduce data exposure, limit sensitive data exchanges and ensure the authenticity of interactions;
- Privacy and data control: users decide which information they share;
- Seamless user experience: fast, passwordless login without disrupting the user journey.
What does this change for me?
As a user: simplicity and security
– Ability to authenticate without a password (no need to remember passwords anymore)
– Reduced risk of fraud and data breaches (my data is no longer centrally stored across multiple sites and applications)
– Full control over my data (I decide what to share)
– A faster and more secure journey (identification and authentication become simpler and safer)
As a website or application: compliance, security and cost reduction
– Improved user experience by removing friction in login journeys (less cart abandonment, smoother onboarding with verified data)
– Reduced support costs (fewer access-related requests) and lower SMS OTP costs (MFA via SMS)
-A unified solution for users across borders, based on a European framework (eIDAS 2, ARF)
– Better GDPR compliance (less stored data means lower risk of data breaches)
The European digital identity can coexist with existing solutions such as MFA and SSO:
- Progressive integration: adding verification options without disrupting current user habits.
- Complementary use cases: for example, a public service may request proof of age via a verifiable credential while still offering traditional authentication methods.
- Objective: strengthen security without forcing abrupt changes in user behavior.
This approach enables more secure and seamless authentication, addressing today’s digital journey challenges.
Architecture and Reference Framework (ARF)
The common architecture of the European digital identity wallet ecosystem is defined in the ARF (Architecture and Reference Framework). It specifies the standards, protocols and data exchange formats between issuers, wallets and service providers (Providers, Relying Parties, etc.).
It provides a structured framework to describe the components and flows involved in:
Issuance: protocols (OpenID4VCI), exchange formats, authorities, and mechanisms such as VC revocation and validity periods;
Holding (wallet): storage, security, consent, and presentation mechanisms (OpenID4VP);
Verification of VCs: verification mechanisms and processes.
Among the key design principles are:
User-centricity and accessibility;
Interoperability (mandatory formats such as ISO/IEC 18013-5 (mDOC) / 23220-2, SD-JWT VC, and optional W3C VCDM 2.0, along with processes and certification);
Privacy by design (selective disclosure of attributes, user consent, minimal data sharing);
Security by design (Wallet Secure Cryptographic Device, Wallet Secure Cryptographic Application, keystore, trust framework).
Compliance with this architecture enables a secure, reliable and user-centric end-to-end journey.
European eIDAS 2.0 regulation: the three key challenges to address before its implementation
The European eIDAS 2.0 regulation requires critical sectors and large platforms to accept the European digital identity by the end of 2027. Until then, three major challenges must be addressed:
- Adoption and trust: raising awareness among users and organizations about the benefits and control over personal data.
- Interoperability: aligning standards such as VC and ARF across public and private stakeholders to ensure a seamless and secure experience, while continuing joint testing initiatives across Europe.
- Compliance: ensuring adherence to principles such as data minimization, explicit consent and data portability.
Decentralized identity and the EUDI Wallet represent a major step forward for web authentication, combining stronger security, ease of use and respect for privacy. They will not replace existing methods overnight, but will complement them, making them more robust and better aligned with user expectations.
The future of authentication no longer relies on passwords, but on verifiable identity credentials controlled by the user.
By adopting this approach, we collectively move toward safer and more reliable digital services.
And you, are you ready to embrace decentralized identity?










Comments (0)
Your email address is only used by Business & Decision, the controller, to process your request and to send any Business & Decision communication related to your request only. Learn more about managing your data and your rights.